Technical methods for the collection, processing and storage of data for ensuring security
 Based on the superordinate question as to how socio-cultural questions influence the acceptance of safety measures, the objective of the sub-project is to expand the undertaking primarily oriented towards the humanities through the addition of technological aspects. One can presume, that the manner in which security technology is used, influences acceptance. Socio-cultural contexts have not been considered sufficiently in technologically-oriented projects to date and the question of acceptance and/or rejection has not been considered to a sufficient extent. The sub-project will evaluate how different technologies are perceived by (an) inhomogeneous audience(s) and their influence on the success of securitization efforts. In the process, the interdependency of social, legal and political factors in connection with security technology will be examined in-depth. Security cultures have several dimensions and the extent to which technical implementation of ideal traditions (e.g. private sphere) is capable of positively influencing trust in technology and technology users must be clarified. Technical methods form the basis for acquiring information superiority and there is a large array of security technologies, which can be used in the public sphere.
Based on the superordinate question as to how socio-cultural questions influence the acceptance of safety measures, the objective of the sub-project is to expand the undertaking primarily oriented towards the humanities through the addition of technological aspects. One can presume, that the manner in which security technology is used, influences acceptance. Socio-cultural contexts have not been considered sufficiently in technologically-oriented projects to date and the question of acceptance and/or rejection has not been considered to a sufficient extent. The sub-project will evaluate how different technologies are perceived by (an) inhomogeneous audience(s) and their influence on the success of securitization efforts. In the process, the interdependency of social, legal and political factors in connection with security technology will be examined in-depth. Security cultures have several dimensions and the extent to which technical implementation of ideal traditions (e.g. private sphere) is capable of positively influencing trust in technology and technology users must be clarified. Technical methods form the basis for acquiring information superiority and there is a large array of security technologies, which can be used in the public sphere.
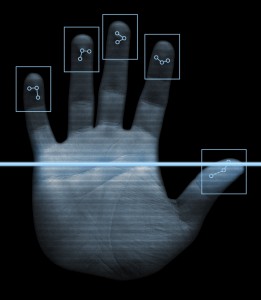
The first goal of the research project is to determine which technologies can be used in a security context in order to influence acceptance and to partition information processing to ensure public security in the following steps: collection, storage, processing and presentation. Technical methods can be used in all steps, which have a positive, but also negative effect on the decision trend of the securitizing move, that is, they are able to positively or negatively influence acceptance.
The goal of the second project phase is to continue to develop select technologies from the first phase according to the suggestions of the project partners. It must be assumed that adequate approaches or approaches in need for improvement do not exist for all areas of the information processing process for securitization. In this case, new concepts will be developed to fill the gap.
The final goal of the third project phase is to combine solutions developed during the second phase in order to create a future-proof overall model that deploys technologies, which contribute to a positive decision trend, in all areas of the processing process. A framework must be created, under which the technologies can be combined in a sensible manner. The modularity of the individual components and high degree of flexibility are important in the process. Only in this way can it be ensured that the methods developed are also future-proof.
Contact:
Hauke Vagts Fraunhofer IOSB Fraunhoferstraße 1 76135 Karlsruhe Tel: +49 721 6091 574 Email: Hauke.vagts@iosb.fraunhofer.de Web: http://www.iosb.fraunhofer.de/servlet/is/29493/?highlight=hauke,vagts
Projekt manager:
Prof. Dr.-Ing. Jürgen Beyerer Fraunhofer IOSB Fraunhoferstraße 1 76131 Karlsruhe Tel: +49 721 6091 210 Email: juergen.beyerer@iosb.fraunhofer.de Homepage: http://www.iosb.fraunhofer.de/servlet/is/11/






